Virtual Business Solutions Blog
Password changes, multi-factor authentication, and countless changes in policy and procedure can make daily workflows more and more complicated. Cybersecurity can truly be a pain—a necessary pain, granted—but a pain nevertheless, and one that can gradually lead to burnout if you aren’t careful. Let’s go over how to mitigate the likelihood of it.
Phishing is a common issue that businesses of all kinds can experience, whether they are a small startup or a large corporation. Hackers are always trying to extol information from your employees, including account credentials, remote access to your systems, and in some cases, funds directly from a bank account. It’s up to you to teach them how to identify and respond to phishing attacks.
Phishing is a remarkably dangerous tactic used by hackers to take advantage of those who might not be quite as in-the-know about security practices. Phishing attacks can be carried out against both businesses and individuals alike, and due to the many different forms these attacks can take—including email, text message, and even fraudulent websites—they can be quite problematic.
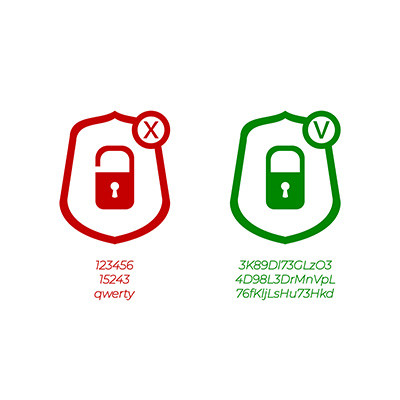
Simple passwords are just not an effective security practice, so if you’re still using credentials like Password, 123456, Guest, or Qwerty, listen up. You need better password hygiene practices before you suffer from a data breach. Here are some ways you can make a better password to protect your business from threats.
There’s no beating around the bush with this one; moving data from one place to another, also known as data migration, is critical to get right the first time. If you create and follow a migration strategy, evaluating here and there to make sure it’s all going according to plan, you’ll see great success in this effort. Let’s go over how you can make it happen.
Depending on the size and complexity of your organization, managing technology can easily become a full-time job. If you are only calling a technician when you are dealing with a computer issue, then you might be sitting on a ticking time bomb. Whether you have internal staff responsible for managing your IT, or you rely on a third-party, you’ll want to make sure the following tasks are getting done.
If you watch technology news, you might notice that there is one day out of every month that gets a lot of attention from the technology sector, and that day is what is called Patch Tuesday. This is the day each month when Microsoft issues all of their patches and security updates, and it’s important to know when this day falls each month—at least, for your IT team it is.
More businesses than ever before are seeing the value of outsourcing their technology management to a managed service provider (MSP) and it’s easy to see why. With a more hands-off approach to technology management, businesses can focus on delivering quality goods and services instead of worrying about their technology. If you are considering jumping on the MSP wagon, consider asking the following questions to make sure you understand what you are getting from your provider.
We’re not shy about sharing how important it is for a business to have comprehensive cybersecurity throughout its entire infrastructure. That’s why we wanted to share what some recent data has shown about the importance of having visibility into your infrastructure.
Spoiler alert: it’s really, really important.
At first glance, cybersecurity might seem incredibly complicated and difficult to understand, but even a baseline understanding of some of the principles of cybersecurity can go a long way toward protecting your business. Let’s discuss some of the common-sense ways you can keep your business secure, even if you don’t have an internal IT department to ask for help from.
In today’s business, sharing files is easy and something many workers take for granted. Unfortunately, not all file-sharing methods are secure. When efficiency is prioritized over security, it can often lead to extremely troublesome situations. For this week’s tip, we thought we’d go through a half dozen practices you can take to ensure your files get to where you need them to get safely and securely.
Since it is our belief that our clients are under constant threat of being the next business hit with a cyberattack, we maintain a pretty aggressive security posture. That’s not to say that all threats are created equal. That’s why it is important to assess risk over the types of attacks and threats you have to confront and plan accordingly.
Your network security is of the utmost importance to your business for numerous, hopefully obvious reasons. However, there are a few errors that are easy enough to make that could easily be the proverbial monkey wrench in the works. Let’s go over what these network security faux pas look like, so you can resolve them more effectively (and don’t worry, we’ll discuss that, too).
While we’re all for efficiency, there are some boundaries that should not be crossed for everyone’s benefit. Take, for instance, the email you use to subscribe to online services. While it may be tempting (or, for some people, automatic) to use your work email address when you sign up for, say, your Netflix account or an online merchant, we wanted to discuss why this is a bad habit to get into that could have lasting consequences.
For every level of business, cybersecurity is a big deal. For the enterprise, they deal with a lot of would-be attacks and need their staff to know how to respond if they are targeted. For the midsize business, the convergence of underwhelming IT support and a growing workforce can be the perfect storm. For the small business, a significant cyberattack could be the beginning of the end for their business. This is why, no matter what size your business is, you need to have a cybersecurity strategy in place that includes tools, monitoring, and protocol. This month, we have put together a list of considerations your business should note to keep your network and data safe.
Whether you’re referring to ransomware, phishing, data theft, spoofing, any of the many forms of cybercrime, it is something that all businesses need to prepare themselves for. While different business sizes will have differing scales to contend with, these kinds of preparations will involve the same basic principles. To help you best defend your company against cybercrime, here are a few tips based on those principles.